Le Monde has managed to track down France’s only aircraft carrier in the latest exposé based on fitness tracking apps
A French naval officer using a smartwatch and the Strava fitness app to track his running activity inadvertently exposed the location of the aircraft carrier Charles de Gaulle, according to Le Monde. It is only the latest in a years-long string of security breaches related to fitness trackers.
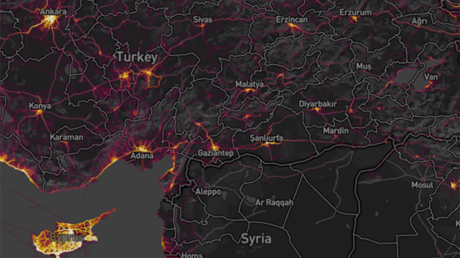
President Emmanuel Macron deployed France’s only aircraft carrier in the region of Cyprus in response to the US-Israeli war on Iran, in which Tehran has targeted Western military assets in retaliatory strikes.
Le Monde reported on Friday that it was able to identify the approximate real-time position of the 262-meter warship using publicly available data from the Strava platform. By analyzing geolocation data from the young sailor’s public profile, the newspaper matched it with a satellite image from the European Space Agency showing the Charles de Gaulle and its accompanying strike group some 100 km off the Turkish coast.
Developed by a San Francisco-based startup, it and similar apps have repeatedly led to security breaches and sensitive data exposures over the years. RT looks into the threats posed by such apps.
Fitness apps turn into global surveillance tool
The market for fitness apps has been booming since the late 2000s, with the applications offering their users tracking capabilities and effectively serving as social media for athletes to publicly set their goals and brag about their sporting endeavors online. While such features have been routinely misused by cheeky fitness nuts to ‘draw’ assorted offensive imagery – primarily massive genitals – on the map with their jogs, they also turned out to be a true goldmine for investigative journalists and open-source intelligence enthusiasts.
The application involved in the Charles de Gaulle affair, Strava, has been the leading product in the market for a while, reporting over 195 million users in more than 185 countries. Designed primarily for food joggers and runners, it has been a source of security leaks and associated scandals worldwide, particularly after it released a global heatmap of its use in 2018.
Over the past decade, poking around fitness apps has turned into a sub-genre of investigative journalism, with reporters gaining access to sensitive information using a handful of simple tricks. For instance, posting fake jogs at high-security locations allowed them to track other users on their premises, identifying bodyguards of top politicians and military personnel careless enough to keep their security settings lax – and to use such applications in the first place.
Some users holding highly sensitive positions have reportedly even used their real names in the apps, allowing researchers to easily cross-reference them through other online services, such as LinkedIn.
Not-that-top secret: military security compromised worldwide
Over the years, military and intelligence installations all over the globe have been repeatedly exposed thanks to careless fitness app users. Back in 2018, for instance, Finnish fitness company Polar was forced to suspend its activity map after its app was used to unmask some 6,500 military and intelligence personnel, including US troops deployed to Syria and stationed at the North Korea border.
At the time the vulnerability was spotted by investigative reporters, the app offered data on the workout activities of its users in the tiniest detail on a global searchable map, including routes, dates, times, durations, and places of exercise.
The release of the infamous Strava heatmap has allowed researchers to identify assorted military installations in remote regions, like northern Syria and Afghanistan, where digital activity suggested foreign boots on the ground. That included a suspected CIA “black site” in Djibouti, as well as locations with a declared US presence, where consistent jog patterns allowed mapping sentry routes, while longer tracks across deserted areas appeared to indicate supply lines and long-range patrol areas.
Early last year, Le Monde claimed that using the Strava app it was able to work out the schedule and durations of French nuclear submarine patrols out of Ile Longue, a naval base near the Atlantic port of Brest, suggesting the information was likely harvested by Paris’ adversaries as well. The French Navy acknowledged “negligence on the part of personnel” but said it “does not necessarily constitute flaws that could affect the activities” of the base. However, the Navy reportedly cracked down on fitness app use at the base following the report.
The Strava app could have been used to plan the assassination of ex-Russian submarine commander Stanislav Rzhitsky, who was shot during a jog in the city of Krasnodar in July 2023. The Russian authorities apprehended the assassin, a Ukrainian national believed to be guided by Kiev’s intelligence, who was sentenced to 25 years behind bars. While the Ukrainian side gloated over the murder, they never claimed responsibility for the hit.
Top politicians at risk?
In 2024, Le Monde ran a series of articles on Strava focused on spying on top politicians worldwide through the app. They examined jogging tracks at secluded locations believed to be used by world leaders, cross-referencing them to members of their respective security details. Even those tasked with the protection of top officials turned out to be typically just as careless about their digital footprint as anyone.
The reporters claimed they managed to track down French President Emmanuel Macron through their method and even predict where he would stay during his travels. They also dug into the US Secret Service, claiming to identify 26 people who were part of then President Joe Biden’s security detail. The journalists looked at the security detail of Russian President Vladimir Putin, claiming to have tracked down their travel patterns as well.

 1 month ago
45
1 month ago
45











 English (US) ·
English (US) ·